“The agencies across the government have acted quickly to mitigate any impact on our fuel supply,” he said.
“We’re prepared to take additional steps depending on how quickly the company is able to bring its pipeline back up to capacity.”
A number of cyber-security researchers, including firms contacted by the BBC, have speculated that the cyber-criminal gang could be Russian, as their software avoids encrypting any computer systems where the language is set as Russian.
Mr Biden said that the US government was concerned about this aspect of the cyber-attack.
“I’m gonna be meeting with President Putin and so far there is no evidence, based on our intelligence people, that Russia is involved,” he said.
“Although, there’s evidence that the actors’ ransomware is in Russia – they have some responsibility to deal with this.”
DarkSide posted a statement on its website on Monday, describing itself as “apolitical”.

“We do not participate in geopolitics, do not need to tie us with a defined government and look for… our motives,” the group said.
The group also indicated it had not been aware that Colonial was being targeted by one of its affiliates, saying: “From today, we introduce moderation and check each company that our partners want to encrypt to avoid social consequences in the future.”
Impact on fuel prices
US fuel prices at the pump rose six cents per gallon on the week to $2.967 per gallon for regular unleaded gasoline, the American Automobile Association (AAA) said on Monday, while Wall Street shares in US energy firms were up 1.5%.
The AAA said prices were heading towards their highest level since 2014.
On Sunday, the US government relaxed rules on fuel being transported by road to minimise disruption to supply. This allowed drivers in 18 states to work extra or more flexible hours when transporting refined petroleum products.
However, there are fears that this could change if the shutdown is prolonged.
Independent oil market analyst Gaurav Sharma told the BBC a lot of fuel was now stranded at refineries in Texas.
“Unless they sort it out by Tuesday, they’re in big trouble,” said Mr Sharma. “The first areas to be hit would be Atlanta and Tennessee, then the domino effect goes up to New York.”
He said oil futures traders were now “scrambling” to meet demand, at a time when US inventories are declining.
Demand – especially for fuel for cars – is on the rise as consumers return to the roads and the economy recovers.
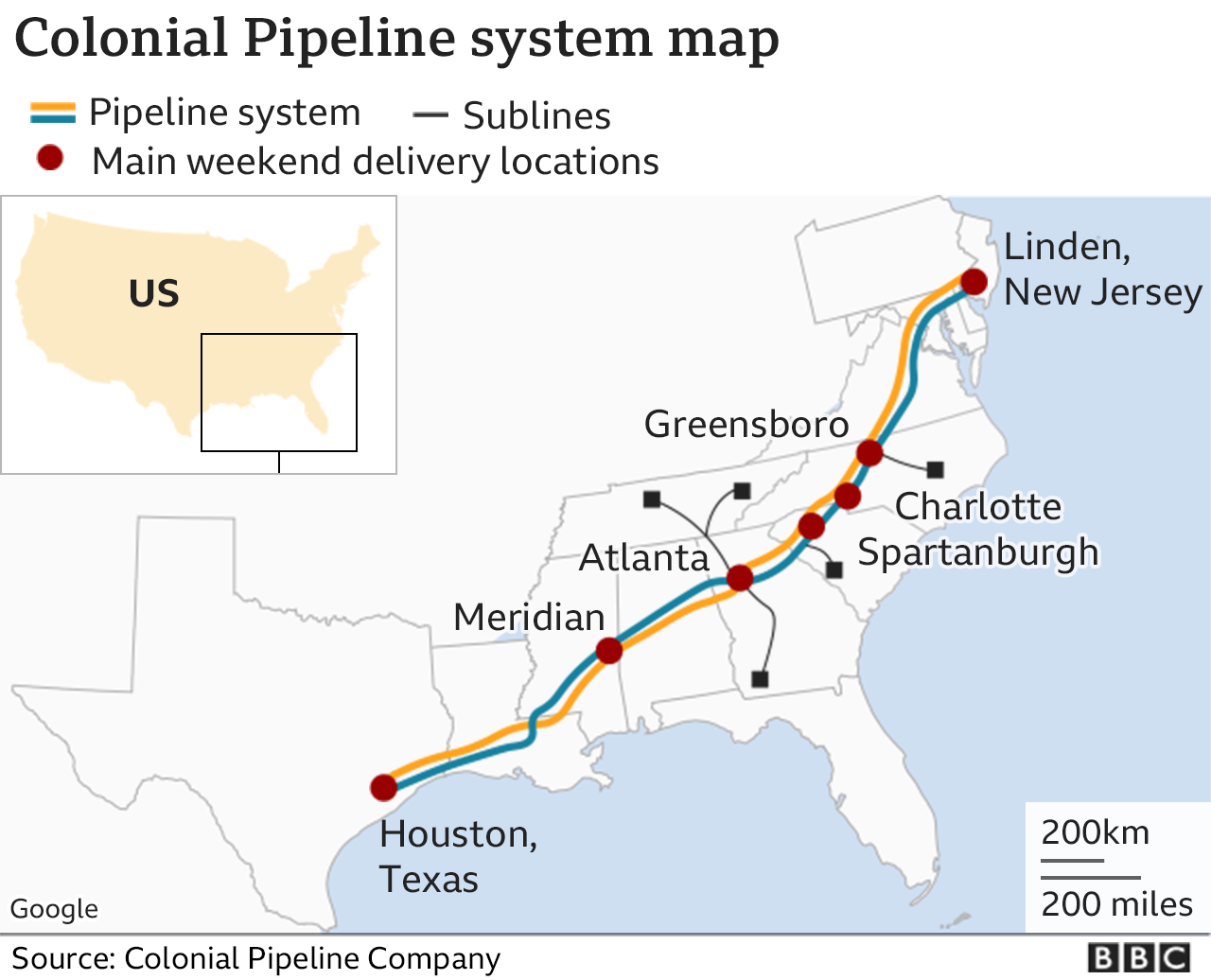
The temporary waiver issued by the Department of Transportation enables oil products to be shipped in tankers up to New York, but this would not be anywhere near enough to match the pipeline’s capacity, Mr Sharma warned.
Sources said the ransomware attack was likely to have been caused by a cyber-criminal gang called DarkSide, who infiltrated Colonial’s network and locked the data on some computers and servers, demanding a ransom on Friday.
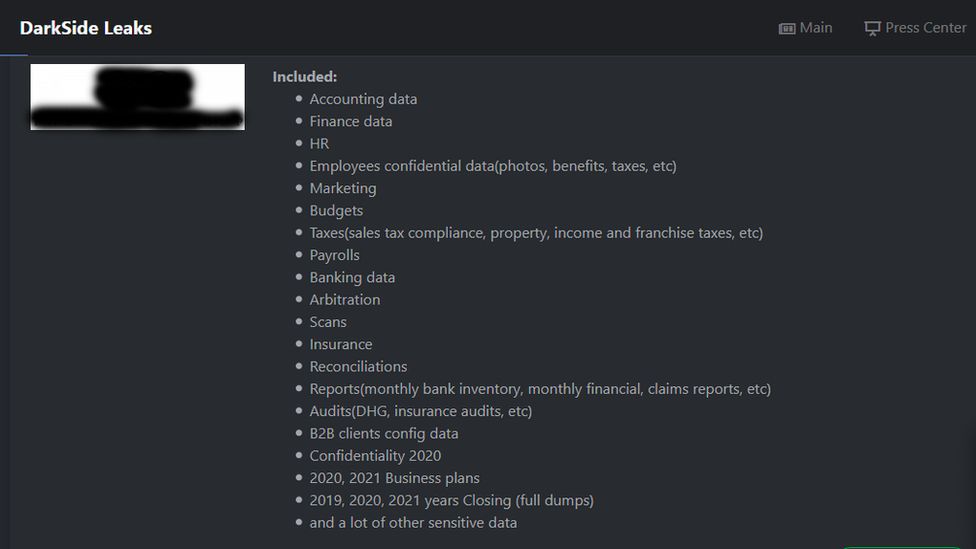
The gang stole almost 100 gigabytes of data hostage, threatening to leak it onto the internet.
The FBI and other government agencies worked with private companies to respond – the cloud computing system the hackers used to collect the stolen data was taken offline on Saturday, Reuters reported.
On Sunday, Colonial said that although its four main pipelines remained offline, some smaller lines between terminals and delivery points were now operational.
“Quickly after learning of the attack, Colonial proactively took certain systems offline to contain the threat. These actions temporarily halted all pipeline operations and affected some of our IT systems, which we are actively in the process of restoring,” the firm said.
It added it would bring its full system back online “only when we believe it is safe to do so, and in full compliance with the approval of all federal regulations”.
Ransomware as a service
The incident highlights the risk ransomware can pose to critical national industrial infrastructure, not just businesses.
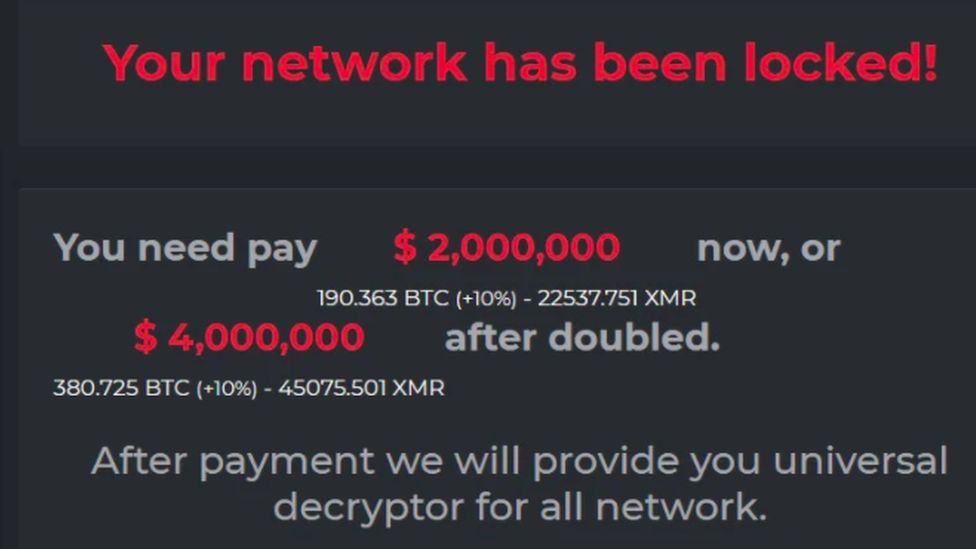
In addition to a notice on their computer screens, victims of a DarkSide attack receive an information pack informing them that their computers and servers are encrypted.
The gang lists all the types of data it has stolen, and sends victims the URL of a “personal leak page” where the data is already loaded, waiting to be automatically published, should the company or organisation not pay before the deadline is up.
DarkSide also tells victims it will provide proof of the data it has obtained, and is prepared to delete all of it from the victim’s network.
According to Digital Shadows, a London-based cyber-security firm, DarkSide operates like a business.
The gang develops the software used to encrypt and steal data from companies.
It then provides ransomware to “affiliates” who pay DarkSide a percentage of their earnings from any successful attacks.
When it released new software in March that could encrypt data faster than before, the gang issued a press release and invited journalists to interview it.
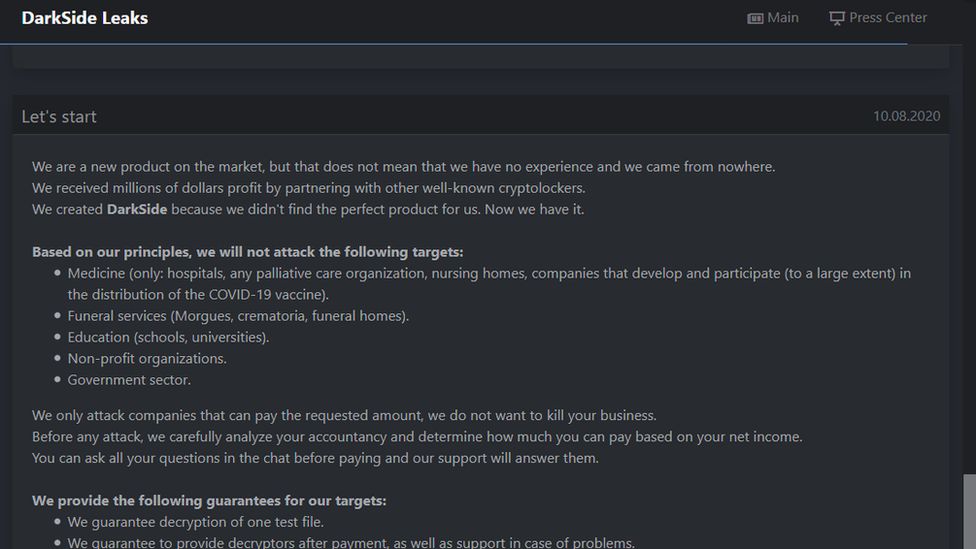
It even has a website on the dark web where it lists all the companies it has hacked and what was stolen, and an “ethics” page where it says which organisations it will not attack.
DarkSide also works with “access brokers” – nefarious hackers who work to harvest the login details for as many working user accounts on various services as they can find.
Rather than break into these accounts and alert users or the service providers, these brokers sit on the usernames and passwords and sell them off to the highest bidders – cyber-criminal gangs who want to use them to carry out much larger crimes.
How did the attack occur?
Digital Shadows thinks the Colonial attack was helped by the coronavirus pandemic, with more engineers remotely accessing control systems for the pipeline from home.
James Chappell, co-founder of Digital Shadows, believes DarkSide could have bought account login details for remote desktop software such as TeamViewer and Microsoft Remote Desktop.
He says it is possible for anyone to look up the login portals for computers connected to the internet on search engines like Shodan, and then “have-a-go” hackers just keep trying usernames and passwords until they get some to work.
“We’re seeing a lot of victims now, this is seriously a big problem,” said Mr Chappell.
“The amount of small businesses that are falling victim to this… It’s becoming a big problem for the economy globally.”
Digital Shadows’ research shows the cyber-criminal gang is likely to be based in a Russian-speaking country, as it avoids attacking companies in post-Soviet states including Russia, Ukraine, Belarus, Georgia, Armenia, Moldova, Azerbaijan, Kazakhstan, Kyrgyzstan, Tajikistan, Turkmenistan and Uzbekistan.